- From: The via GitHub <sysbot+gh@w3.org>
- Date: Mon, 08 Mar 2021 09:11:44 +0000
- To: public-webauthn@w3.org
thedreamwork has just created a new issue for https://github.com/w3c/webauthn: == <new proposal> Extending WebAuthn Protocol for Remote Authentication == Modern identification techniques ask users to scan their ID documentation or do face verification authentication in order to be verified by an online service. Such techniques request from users to capture a photo through the camera of their mobile device. Data authenticity and fidelity is crucial for user identification techniques. Therefore, it is vital to address feasible attacks. Here we will concentrate on one such attack — the injection attack. Such attacks are easy to perform, devastatingly successful, and represent a significant barrier to the widespread deployment of authentication systems that use consumer smart devices in web scenario. Instead of attacking the system in front of the capture device (e.g., the webcam on a smart device), the injection attack operates by copying a digital representation of a real biometric signal, and then injecting it into the system at some later date and/or different location. Since the copied signal is bit-for-bit an exact replica of a legitimate signal, it can completely bypass the security checks, such as liveness and anti-spoofing. One of the most important goal is the ability of the remote service to verify the authenticity of the received data. In our proposal, remote image attestation utilizes a modified Webauthn protocol to facilitate a public-key signatures between the client and the server, means that you have the private key and you share a public key with the verifier of the signature. When a photo has been captured, it computes and signs the hash of the photo with the private key. When the user submits the photo, the server computes the hash of the photo with the same hash function as the client side and using the public key for the corresponding user verifies that the signed hash matches the hash of the received photo. If this is successful, then the uploaded photo has not been tampered with, otherwise it is potentially dangerous to trust the client with camera data. Image Attest is actually an extension to WebauthN API. Image Attest is an API for protecting media authenticity. In the nutshell it is an interface to talk to media producer. You give it a challenge. You get safe media back. There are two operations: MakeCredential and GenerateImageAssertion 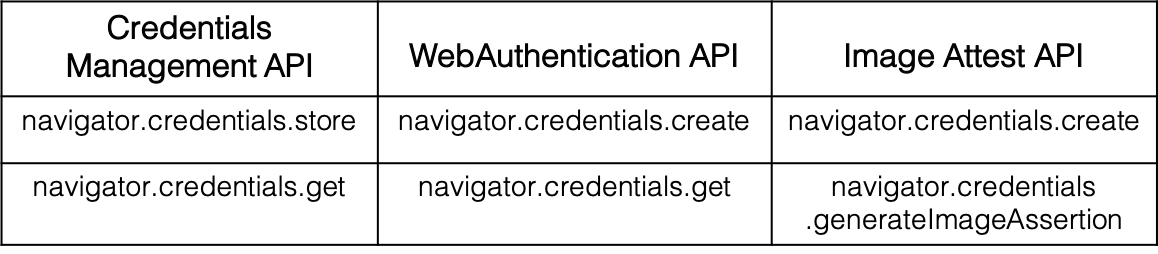 Using the navigator.credentials.create call to create a cryptographic key on device, and then attest to the key’s validity. This produces an attestation object that website passes to server, along with the corresponding key identifier. Server verifies the attestation object, and then extracts the embedded public key and other information. Later, Server uses the key to verify assertion objects with camera data using navigator.credentials.generateImageAssertion call. Here are our updated thoughts on the remote authentication as of early Match. This document should explain most of what we're thinking. [Ensuring the Authenticity and Fidelity of Camera data.pdf](https://github.com/w3c/webauthn/files/6100160/Ensuring.the.Authenticity.and.Fidelity.of.Camera.data.pdf) Please view or discuss this issue at https://github.com/w3c/webauthn/issues/1580 using your GitHub account -- Sent via github-notify-ml as configured in https://github.com/w3c/github-notify-ml-config
Received on Monday, 8 March 2021 09:11:46 UTC