- From: Leonard Rosenthol <lrosenth@adobe.com>
- Date: Mon, 9 Aug 2021 12:42:38 +0000
- To: "Michael Herman (Trusted Digital Web)" <mwherman@parallelspace.net>, "public-credentials@w3.org" <public-credentials@w3.org>
- Message-ID: <MN2PR02MB699266145C0F2304BF119E9ACDF69@MN2PR02MB6992.namprd02.prod.outlook.com>
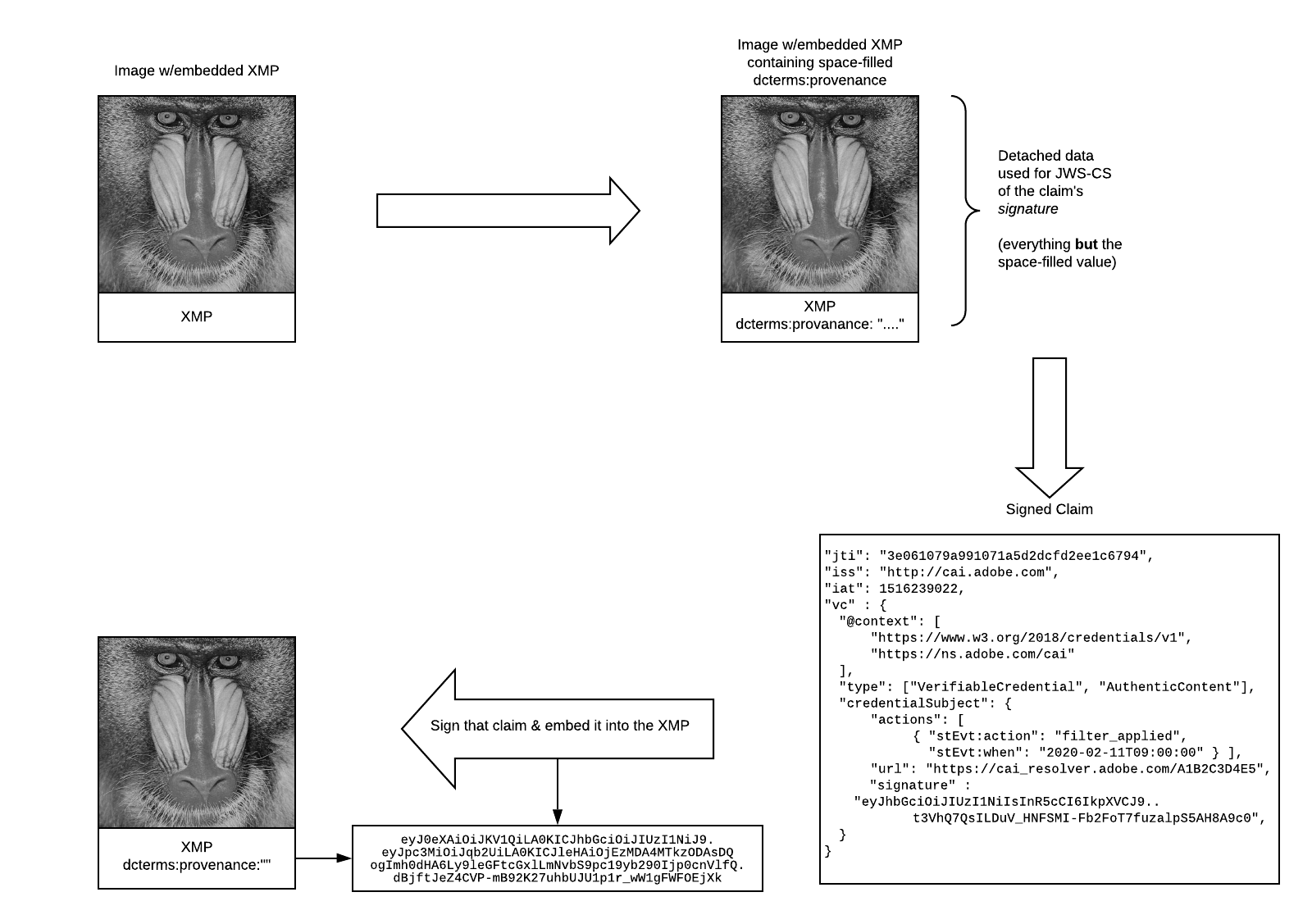
Michael – Thanks for taking the time to experiment with this. You are (for the most part) where we were two years ago when we first started down the path towards architecting the technology behind the Content Authenticity Initiative. Like you, we had hoped to be able to do everything with XMP and VC. I found this old image from our original prototype that should feel familiar 😉. [Timeline Description automatically generated with low confidence] While this method works, for the most part, for raster images with a single claim/credential – it immediately breaks down in pretty much any other workflow. Whether it is the image going through normal editing & publishing flows (e.g. Camera->Photoshop->Twitter) or being used as an ingredient in a multi-image combined scenario (e.g., placing one image into another). And when you get to other asset types – video, documents, 3D, etc. more and more problems ensue. Which is why we ended up having to moving away from that approach. But at the end of the day, we are still using VC’s for what they were intended to accomplish (identity and accomplishments) as part of our larger attribution system. You can learn about it at https://contentauthenticity.org/how-it-works and keep an eye on https://c2pa.org where we will be making more technical material available shortly. Leonard From: Michael Herman (Trusted Digital Web) <mwherman@parallelspace.net> Date: Monday, August 9, 2021 at 1:49 AM To: Leonard Rosenthol <lrosenth@adobe.com>, public-credentials@w3.org <public-credentials@w3.org> Subject: VC-if-eye a plain old .JPG file [was: Binding credentials to publicly accessible repositories] RE: There is no mechanism in XMP nor in most standard asset formats for establishing a model for tamper evidence, such as Digital Signatures, (H)MAC, etc Leonard here’s a counterexample. I’ve applied to the principles and data model for Structured Credentials (https://www.youtube.com/watch?v=FFv4WZ0p3aY&list=PLU-rWqHm5p45dzXF2LJZjuNVJrOUR6DaD&index=1<https://nam04.safelinks.protection.outlook.com/?url=https%3A%2F%2Fwww.youtube.com%2Fwatch%3Fv%3DFFv4WZ0p3aY%26list%3DPLU-rWqHm5p45dzXF2LJZjuNVJrOUR6DaD%26index%3D1&data=04%7C01%7Clrosenth%40adobe.com%7C7fdcc84d58ee48bada8008d95af932f8%7Cfa7b1b5a7b34438794aed2c178decee1%7C0%7C0%7C637640849953426744%7CUnknown%7CTWFpbGZsb3d8eyJWIjoiMC4wLjAwMDAiLCJQIjoiV2luMzIiLCJBTiI6Ik1haWwiLCJXVCI6Mn0%3D%7C2000&sdata=d8uSetTRtyT8OQpHNq1uCTd3wZstK7adKC7tdmP1qgE%3D&reserved=0>) to VC-if-eye a plain old .JPG file (a photo I took with my Pixel 4a phone). * Test1_original.jpg is the original, unmodified test copy of the photo * Test1_ps1.txt is a script that uses exiftool.exe to add the Structured Credential structures to the original test copy of the photo …including the proof elements stored in the EnvelopeSeal structure. They are stored as elements in the XMP Keyword Info property of the photo. * Test1_xmp.png is a screen shot of the Structured Credential structures embedded into the XMP Keyword Info properties of the photo. We now have a mechanism for a .JPG file (or any XMP compatible media file) to serve as both a photo and a Verifiable Credential. We are now able to VC-if-eye any XMP compatible media file. Any holes? Best regards, Michael Herman Far Left Self-Sovereignist Self-Sovereign Blockchain Architect Trusted Digital Web Hyperonomy Digital Identity Lab Parallelspace Corporation [cid:image002.jpg@01D78CFA.80E0AE80] From: Leonard Rosenthol <lrosenth@adobe.com> Sent: August 3, 2021 3:02 PM To: Michael Herman (Trusted Digital Web) <mwherman@parallelspace.net>; public-credentials@w3.org Subject: Re: Binding credentials to publicly accessible repositories There is no mechanism in XMP nor in most standard asset formats for establishing a model for tamper evidence, such as Digital Signatures, (H)MAC, etc. Leonard From: Michael Herman (Trusted Digital Web) <mwherman@parallelspace.net<mailto:mwherman@parallelspace.net>> Date: Tuesday, August 3, 2021 at 2:49 PM To: public-credentials@w3.org<mailto:public-credentials@w3.org> <public-credentials@w3.org<mailto:public-credentials@w3.org>>, Leonard Rosenthol <lrosenth@adobe.com<mailto:lrosenth@adobe.com>> Subject: Re: Binding credentials to publicly accessible repositories Leonard, how do you define "native tamper-evident system"? Get Outlook for Android<https://nam04.safelinks.protection.outlook.com/?url=https%3A%2F%2Faka.ms%2FAAb9ysg&data=04%7C01%7Clrosenth%40adobe.com%7C7fdcc84d58ee48bada8008d95af932f8%7Cfa7b1b5a7b34438794aed2c178decee1%7C0%7C0%7C637640849953426744%7CUnknown%7CTWFpbGZsb3d8eyJWIjoiMC4wLjAwMDAiLCJQIjoiV2luMzIiLCJBTiI6Ik1haWwiLCJXVCI6Mn0%3D%7C2000&sdata=AuKbKnfOaxufo32nVhnw%2FK2mV7bYDVA5YA01ewOuIX0%3D&reserved=0> ________________________________ From: Leonard Rosenthol <lrosenth@adobe.com<mailto:lrosenth@adobe.com>> Sent: Tuesday, August 3, 2021 10:53:47 AM To: Michael Herman (Trusted Digital Web) <mwherman@parallelspace.net<mailto:mwherman@parallelspace.net>>; public-credentials@w3.org<mailto:public-credentials@w3.org> <public-credentials@w3.org<mailto:public-credentials@w3.org>> Subject: Re: Binding credentials to publicly accessible repositories Michael, thanks for the reference to XMP…but you are probably not aware that I am the chair of ISO TC 171/SC 2/WG 12 where XMP is standardized *and* the project leader for XMP itself. (oh, and I am also the XMP Architect internally to Adobe 😉 ). So yes, leveraging existing open standards such as XMP is indeed a key to delivering on the promises mentioned below – but it can’t be the only solution due to it being a text-based serialization (thus not lending itself well to binary data structures) and not having a native tamper-evident system. Additionally, while it is supported by most common asset formats, it is not supported by all. Leonard From: Michael Herman (Trusted Digital Web) <mwherman@parallelspace.net<mailto:mwherman@parallelspace.net>> Date: Tuesday, August 3, 2021 at 10:43 AM To: Leonard Rosenthol <lrosenth@adobe.com<mailto:lrosenth@adobe.com>>, public-credentials@w3.org<mailto:public-credentials@w3.org> <public-credentials@w3.org<mailto:public-credentials@w3.org>> Subject: Re: Binding credentials to publicly accessible repositories Checkout https://en.wikipedia.org/wiki/Extensible_Metadata_Platform<https://nam04.safelinks.protection.outlook.com/?url=https%3A%2F%2Fen.wikipedia.org%2Fwiki%2FExtensible_Metadata_Platform&data=04%7C01%7Clrosenth%40adobe.com%7C7fdcc84d58ee48bada8008d95af932f8%7Cfa7b1b5a7b34438794aed2c178decee1%7C0%7C0%7C637640849953436697%7CUnknown%7CTWFpbGZsb3d8eyJWIjoiMC4wLjAwMDAiLCJQIjoiV2luMzIiLCJBTiI6Ik1haWwiLCJXVCI6Mn0%3D%7C2000&sdata=D8nz7ROeW3pnazqtZyt%2BJIJMp4IbhojlAGn5h6F6PVA%3D&reserved=0> And here's a data model to consider for use in a custom XMP profile: https://youtu.be/FFv4WZ0p3aY<https://nam04.safelinks.protection.outlook.com/?url=https%3A%2F%2Fyoutu.be%2FFFv4WZ0p3aY&data=04%7C01%7Clrosenth%40adobe.com%7C7fdcc84d58ee48bada8008d95af932f8%7Cfa7b1b5a7b34438794aed2c178decee1%7C0%7C0%7C637640849953446653%7CUnknown%7CTWFpbGZsb3d8eyJWIjoiMC4wLjAwMDAiLCJQIjoiV2luMzIiLCJBTiI6Ik1haWwiLCJXVCI6Mn0%3D%7C2000&sdata=63YZ3dftM%2FJojnSw5urE%2FLJEKcTonpksdz5oi5F9oIk%3D&reserved=0> Get Outlook for Android<https://nam04.safelinks.protection.outlook.com/?url=https%3A%2F%2Faka.ms%2FAAb9ysg&data=04%7C01%7Clrosenth%40adobe.com%7C7fdcc84d58ee48bada8008d95af932f8%7Cfa7b1b5a7b34438794aed2c178decee1%7C0%7C0%7C637640849953446653%7CUnknown%7CTWFpbGZsb3d8eyJWIjoiMC4wLjAwMDAiLCJQIjoiV2luMzIiLCJBTiI6Ik1haWwiLCJXVCI6Mn0%3D%7C2000&sdata=YMkjvKTAr2tTeNsis75ShPmswNh618Hs%2BTr50ltVCsw%3D&reserved=0> ________________________________ From: Michael Herman (Trusted Digital Web) <mwherman@parallelspace.net<mailto:mwherman@parallelspace.net>> Sent: Friday, July 30, 2021 1:25:18 PM To: Leonard Rosenthol <lrosenth@adobe.com<mailto:lrosenth@adobe.com>>; public-credentials@w3.org<mailto:public-credentials@w3.org> <public-credentials@w3.org<mailto:public-credentials@w3.org>> Subject: RE: Binding credentials to publicly accessible repositories So an alternate strategy to avoid embed an actual VC or otherwise try to attach a VC to an asset is to use the metadata capabilities of each of these formats to store the credential id, @context, vc type list, credentialSubject id, the individual claims (name-value pairs), and the proof elements …vc-if-eye each format using each format’s native metadata capabilities. From: Leonard Rosenthol <lrosenth@adobe.com<mailto:lrosenth@adobe.com>> Sent: July 30, 2021 1:03 PM To: Michael Herman (Trusted Digital Web) <mwherman@parallelspace.net<mailto:mwherman@parallelspace.net>>; public-credentials@w3.org<mailto:public-credentials@w3.org> Subject: Re: Binding credentials to publicly accessible repositories Michael – not sure you understand the scenario here. We aren’t building a specific system/solution for our own needs and those of our customers – we are developing an open standard that associates provenance with existing assets (eg. JPEG, PNG, MP4, PDF, etc.). Since those are the formats that are recognized by systems (and regulatory solutions) today, it would make no sense to start wrapping them in some other format (be it JSON, XML, or whatever). JPEG files (for example) need to work everywhere they do today – BUT contain tamper-evident provenance. Leonard From: Michael Herman (Trusted Digital Web) <mwherman@parallelspace.net<mailto:mwherman@parallelspace.net>> Date: Friday, July 30, 2021 at 2:46 PM To: Leonard Rosenthol <lrosenth@adobe.com<mailto:lrosenth@adobe.com>>, public-credentials@w3.org<mailto:public-credentials@w3.org> <public-credentials@w3.org<mailto:public-credentials@w3.org>> Subject: RE: Binding credentials to publicly accessible repositories It’s a SMOP (small matter of programming). Once upon a time, browers weren’t capable of displaying a lot of different kinds of resources (e.g. XML). Why not render your VCs as XML? …or consider using server-side rendering? …or write an in-browser renderer using WASM? “The difficult we can do, the impossible takes us a little bit longer…” 😊 From: Leonard Rosenthol <lrosenth@adobe.com<mailto:lrosenth@adobe.com>> Sent: July 30, 2021 12:35 PM To: Michael Herman (Trusted Digital Web) <mwherman@parallelspace.net<mailto:mwherman@parallelspace.net>>; public-credentials@w3.org<mailto:public-credentials@w3.org> Subject: Re: Binding credentials to publicly accessible repositories Given that putting a “.vc” file on a website or in a Twitter feed of YouTube channel isn’t going have it properly displayed – that’s not an option, unfortunately, Michael. Leonard From: Michael Herman (Trusted Digital Web) <mwherman@parallelspace.net<mailto:mwherman@parallelspace.net>> Date: Friday, July 30, 2021 at 1:05 PM To: Leonard Rosenthol <lrosenth@adobe.com<mailto:lrosenth@adobe.com>>, public-credentials@w3.org<mailto:public-credentials@w3.org> <public-credentials@w3.org<mailto:public-credentials@w3.org>> Subject: RE: Binding credentials to publicly accessible repositories I suggest storing the “original version” of the artwork as a claim within a signed credential …the credential wraps the artwork like a container or a “frame”. I believe this is much better than trying to attach a credential to the artwork. Best regards, Michael Herman Far Left Self-Sovereignist Self-Sovereign Blockchain Architect Trusted Digital Web Hyperonomy Digital Identity Lab Parallelspace Corporation [cid:image003.jpg@01D78CFA.80E0AE80] From: Leonard Rosenthol <lrosenth@adobe.com<mailto:lrosenth@adobe.com>> Sent: July 30, 2021 10:31 AM To: public-credentials@w3.org<mailto:public-credentials@w3.org> Subject: Binding credentials to publicly accessible repositories I realize that I might be out on the bleeding edge a bit, though not completely as I think it is very similar to what OpenBadges will face as they move to VC’s… In the Trust Model section of the VC Data Model spec, it states that one of aspects of that model is: The holder trusts the repository to store credentials securely, to not release them to anyone other than the holder, and to not corrupt or lose them while they are in its care. This is certainly true when the repository in question is something like a wallet that is designed to be kept private or local (not shared). But what happens when the repository is designed to be out in the public… such as an image or PDF with the VC embedded? As part of the C2PA’s (https://c2pa.org<https://nam04.safelinks.protection.outlook.com/?url=https%3A%2F%2Fc2pa.org%2F&data=04%7C01%7Clrosenth%40adobe.com%7C7fdcc84d58ee48bada8008d95af932f8%7Cfa7b1b5a7b34438794aed2c178decee1%7C0%7C0%7C637640849953456611%7CUnknown%7CTWFpbGZsb3d8eyJWIjoiMC4wLjAwMDAiLCJQIjoiV2luMzIiLCJBTiI6Ik1haWwiLCJXVCI6Mn0%3D%7C2000&sdata=4vKDfI6ZCOKCzCQ6ZhSDBhTmsZ6%2FUYyGEZfzFRQ7Xmw%3D&reserved=0>) work on establishing provenance for digital assets, we will be using VC’s as a way for persons and organizations to establish their relationships to the asset. Specifically in this instance, we’re extending schema.org’s Person and Organization schemas, as used by their CreativeWork schema, to support referencing a VC. This then allows the author or publisher (or any of the other roles in CW) to provide their credentials in that role, which (a) adds useful trust signal(s) to the end consumer and (b) helps establish reputation. These VC’s (etc.) will be embedded into the assets (e.g., video, images, documents, etc.) in a tamper-evident manner, so that in addition to the individual VC’s “proof”, any attempt to change the CreativeWork relationships, etc. can also be detected. This all works great. However, in doing some threat modelling, we recognized that we have no protection against a malicious actor simply copying the VC from one asset and dropping it into another (and then signing the new setup), because there is nothing that binds the credential to the asset in our case. Has anyone run into this scenario before and has some guidance to offer? Am I doing something that I shouldn’t be doing – and if so, what does that mean for OpenBadges? All thoughts and suggestions welcome! Thanks, Leonard
Attachments
- image/png attachment: image001.png
- image/jpeg attachment: image002.jpg

- image/jpeg attachment: image003.jpg

Received on Monday, 9 August 2021 12:43:04 UTC